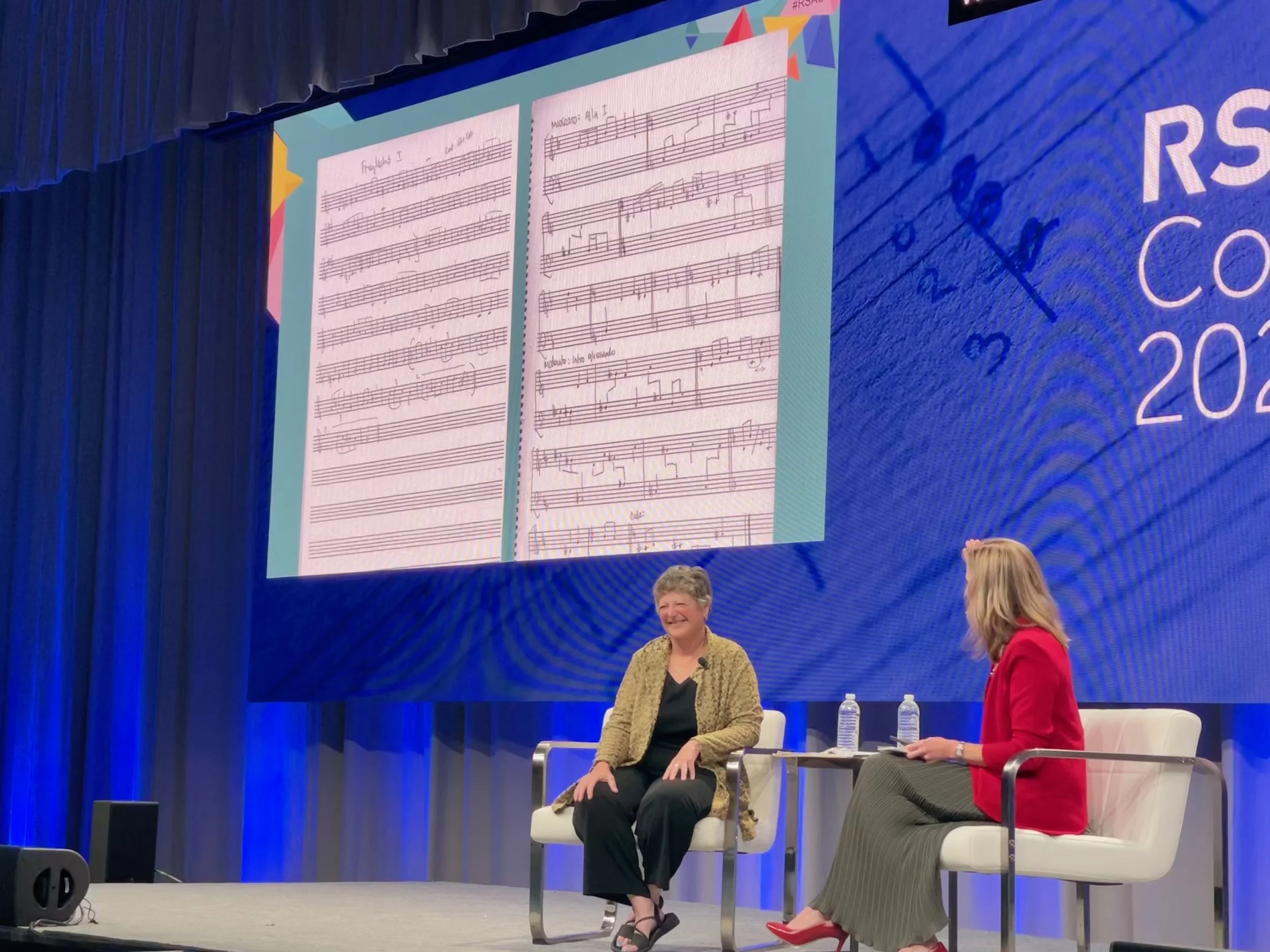
If you told me a year ago that I would meet a cold war hero at a birthday party, I wouldn’t have believed you. And I would be even more skeptical if you told me she would be an unintimidating, approachable music professor with an infectious smile. It’s the summer of 2021. After more than a year…
log4shell
UPDATED December 16, 2021
If you are reading this, you likely have heard about Log4Shell, the December, 2021 critical zero-day remote-code execution vulnerability in the popular Log4j software library that is developed and maintained by the Apache Software Foundation. Apache has patched this vulnerability in version 2.15.0, however vendors who use this library will need to…
Hacking Humble Bundle
Last year, Humble Bundle teamed up with the great tech publisher, No Starch Press, to offer deeply discounted hacking ebooks for as little as one dollar with the Hacking 101 By No Starch Press Humble Bundle of ebooks. This year, on Giving Tuesday, No Starch Press has a new Hacking Book Bundle. The regular cost for the ebooks is more than $800 but you can get all of these ebooks for thirty dollars or just a few of the ebooks for as little as one dollar.
Cybersecurity Awareness Month 2021
October is Cybersecurity Awareness Month and Breast Cancer Awareness Month. Since this is a cybersecurity blog, we will focus on cybersecurity but let’s take a moment to talk about the important topic of breast cancer.
Colonial Pipeline: Lessons Learned
The Colonial Pipeline ransomware attack took down the largest fuel pipeline in the United States and resulted in consumer hoarding of fuel and a short-term shortage of gasoline on the east coast of the U.S.. What could they have done to prevent this attack and what can you do today to prevent a similar attack?
President Biden's Cybersecurity Executive Order
Aiming to improve cybersecurity in the United States, President Biden signed an executive order (EO) on May 12, 2021. Although the EO focuses on U.S. federal departments’ and agencies’ cybersecurity, it will likely result in standards that will change the way the private sector manages cybersecurity within the United States and globally.
This cybersecurity EO was signed soon after the world experienced a series of widespread cybersecurity incidents such as…
World Password Day - May 6, 2021
It’s World Password Day!
Are your passwords strong enough?
Do you have a long, unique password for every account?
Do you use multi-factor authentication where available?
If you answered, “no” to any of these questions…
Facebook Leak Leads To Smishing
I have always considered myself pretty lucky in that I rarely receive fraudulent text messages. That luck recently ran out. Over the past few weeks I have noticed an uptick in the number of SMS phishing (smishing) messages that I receive on my phone. A few days ago, the smishing seemed to become even more frequent…
2021 Cybersecurity Report Roundup
Annual cybersecurity reports are a rich resource of statistics and information for cybersecurity professionals, academics, journalists and anyone who is interested in cybersecurity. Below is a categorized list of many of these reports…
2021 Top Cybersecurity Leaders
The March 2021 issue of Security magazine, partnering with (ISC)2, featured their inaugural list of the Top Cybersecurity Leaders for 2021. As the author of this blog, I am both humbled and honored, to not only be part of the inaugural team, but also to be recognized with these accomplished cybersecurity professionals.
ILoveYou.txt.vbs
Since today is known for love, let’s look back 21 years to one of the more destructive, costly and famous viruses in history. The “ILoveYou” worm, also known as the “Love Bug” or “Love Letter For You” infected more than ten million Windows computers, beginning on May 5, 2000. This worm began spreading as an email message with the subject line "ILOVEYOU" and the attachment "LOVE-LETTER-FOR-YOU.txt.vbs".
Safer Internet Day 2021
Tuesday, February 9th, 2021, marks the 18th edition of Safer Internet Day with the theme "Together for a better Internet." Safer Internet Day (SID) started as an EU SafeBorders project in 2004 and is now celebrated in approximately 170 countries worldwide. Each February…
Happy New Year!
2020 was a difficult year and Between The Hacks wants to congratulate everyone who pulled through the challenges. We have all lived through a year that delivered a global pandemic, civil unrest, and a controversial …
Merry Christmas & Happy Holidays
Merry Christmas and Happy Holidays from Between The Hacks!
Whether you celebrate Christmas, Hanukkah, Kwanza or Festivus, we hope you and your family are doing well, staying healthy and surviving 2020…
BTH News 20December2020
This week on Between The Hacks: The SolarWinds hack explained in plain English, D-Link router vulnerabilities, Google explains their global outage, 28 malware-infected browser extensions and cybercrime book for the security enthusiast on your gift list.
SolarWinds Hack: The Basics
By now you have probably heard about the SolarWinds supply-chain compromise that has impacted government and businesses all over the world. This story is still unfolding so I won’t try to explain everything in detail, rather, I’ll attempt to explain the situation for the less-technical reader and link to some resources so that you can follow the story.
BTH News 13December2020
This week on Between The Hacks: A dental data breach, the U.S. IoT Security Law, a 2020 Microsoft vulnerability report, the final sunset of Adobe Flash, Rebooting by Lisa Forte and the Smashing Security Christmas party.
The U.S. IoT Cybersecurity Improvement Act Becomes Law
An important step toward securing the Internet was achieved on December 4, 2020, when President Trump signed an IoT security bill into law. The Internet of Things Cybersecurity Improvement Act of 2020 has been in the works since 2017 and was passed by the U.S. House of Representatives in September 2020 and the U.S. Senate in November 2020.
The bi-partisan team that backed the IoT bill included…
HACKING 101 Humble Bundle
Now that Black Friday and Cyber Monday are over, you may still be searching for some great deals. If so, you’ll hardly find a better deal than this one. Humble Bundle has teamed up with the great tech publisher, No Starch Press, to offer deeply discounted hacking e-books for as little as one dollar.
HAPPY THANKSGIVING 2020
Between The Hacks would like to thank all of those who read, share, and make this blog possible. Please have a safe and happy Thanksgiving and be secure when shopping this holiday season.