Password Managers (The Password Conundrum: Part 2)
In Part 1 of the Password Conundrum, we talked about how we all hate passwords and how the crazy cybersecurity wonks tell us that we have to do unreasonable things like:
Make passwords that are so complex that you can’t possibly remember them (long and multiple character sets)
Make a unique password for every one of the 10’s or hundreds of sites and applications that we use. Oh, and they all have to be long and strong which means we won’t remember them.
Today we are going to explore how you can achieve this and actually make your digital life more secure and much easier than back when you had to remember all of those passwords or look them up on a spreadsheet on your computer’s desktop (YIKES!). Enter… the Password Manager!
Password Managers
A Password Manager is a software tool that is used to store all of your passwords in an encrypted file so that you have very easy access to them, but nobody else can get access. Most modern password managers have additional features such as cloud storage, auto-filling fields and password generators that make very good passwords.
The cloud storage feature of password managers provides easy access to your passwords from different devices. While it sounds scary to have all of your passwords stored online, a good password manager will encrypt all of your password data before it is uploaded to the cloud and will make sure that only you have the keys (the master password that you set) to decrypt your passwords on each device. However, all of this security it great unless you forget your master password, in that case, you lose everything.
The autofill feature is convenient because when you go to a site, such as LinkedIn, the password manager’s browser plugin recognizes the URL and sees the username and password fields, then enters your username and password automatically. This is not only convenient, but it also helps defend against keystroke logging malware from learning and sharing your passwords. It also ensures that your username and password are not entered into a doppelgänger domain website, like 1inkedin.com rather than linkedin.com. This feature has however, been abused and used for some creative attacks. By hiding the username/password fields on a web page that are not viewable by the person visiting that page, some attackers have been able to harvest account credentials. This Wired article goes into greater detail around the attack.
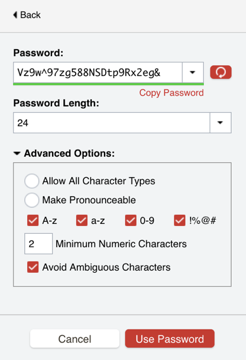
The password generator is a very important part of this whole solution. The password manager can’t help you much if you create simple passwords such as 12345678 or monkey123. So, the password manager will recommend passwords for you and if you accept them when creating an account, it will automatically store that in your password manager. For example, here is a screenshot from the password generator in LastPass. You can see that it is 24 characters and is using all four-character sets (uppercase, lowercase, numbers and special characters) to create a difficult password to guess and a nearly impossible password to remember. Good thing you don’t need to remember or ever know this password!
There is certainly debate over the problems with password managers, such as what if you forget your master password, or what if someone gets your master password? These are valid arguments, however, with the rapid growth of account compromises and data breaches, the risk seems far greater that someone is using simple passwords and trying to remember them or reusing those passwords on multiple accounts.
Below, I listed some of the common password management strategies that people use today. The ratings are based on my personal opinion and backed up by no real science or research, however I have scored the risk levels and explained the reason for the scores. The scores go from 0 – Low Risk to 10 – Very High risk
Reusing simple passwords (e.g. monkey123) – 10 Very High risk because it is easy to guess (by guessing, I mean using a super fast password cracking/guessing tool).
Reusing complex passwords (My dog likes to eat at 8 a.m.) – 8 HIGH risk because while the password is good, if anyone guesses or learns it, they can use it on other sites as well. (e.g. If your LinkedIn password is discovered, the bad guys/gals will try that username and password on every social media and popular website to see if you used it elsewhere)
Saving unique passwords in an unencrypted document or spreadsheet on your computer – 6 Medium While you are protected against someone getting access to your passwords document unless they are logged in to your computer, if someone does get access to your files or your backups or malware gives access to an attacker, Game Over.
Creating unique but predictable complex passwords for each account - (e.g. Facebook**pw4224) – 6 Medium These are good passwords expect that if someone gets one of your passwords, they can likely figure out the rest of your passwords.
Writing all of your passwords in a book and keeping it locked up – 4 Medium/Low but only if the book is properly secured. Locked in a desk at your house is much better than locked in a desk at work. Also, if there is a fire or flood, you lose all of your passwords.
Using a password manager with unique, complex passwords for every site – 1 Low. The risks here are if you forget your master password or if someone else gets your master password.
Since I have tried only a few password managers and not tested them all equally, I’ll leave the evaluations to others. I will say that I have been a happy LastPass user for many years but please decide on your own, which works best for you. Here are a few articles that compare and contrast the leading password managers.
https://www.consumersadvocate.org/password-manager
https://www.pcmag.com/article2/0,2817,2407168,00.asp
https://www.wired.com/story/password-manager-autofill-ad-tech-privacy/
https://lifehacker.com/5529133/five-best-password-managers
[Added June 2020] https://www.zdnet.com/article/best-password-managers/
In closing, I’ll say that password managers will greatly help to secure your accounts, but are they enough? In Part 3 of the blog series on passwords, I’ll explain Multi-Factor Authentication (MFA) and how and why you should use it almost everywhere you can.